Is our critical infrastructure secure?
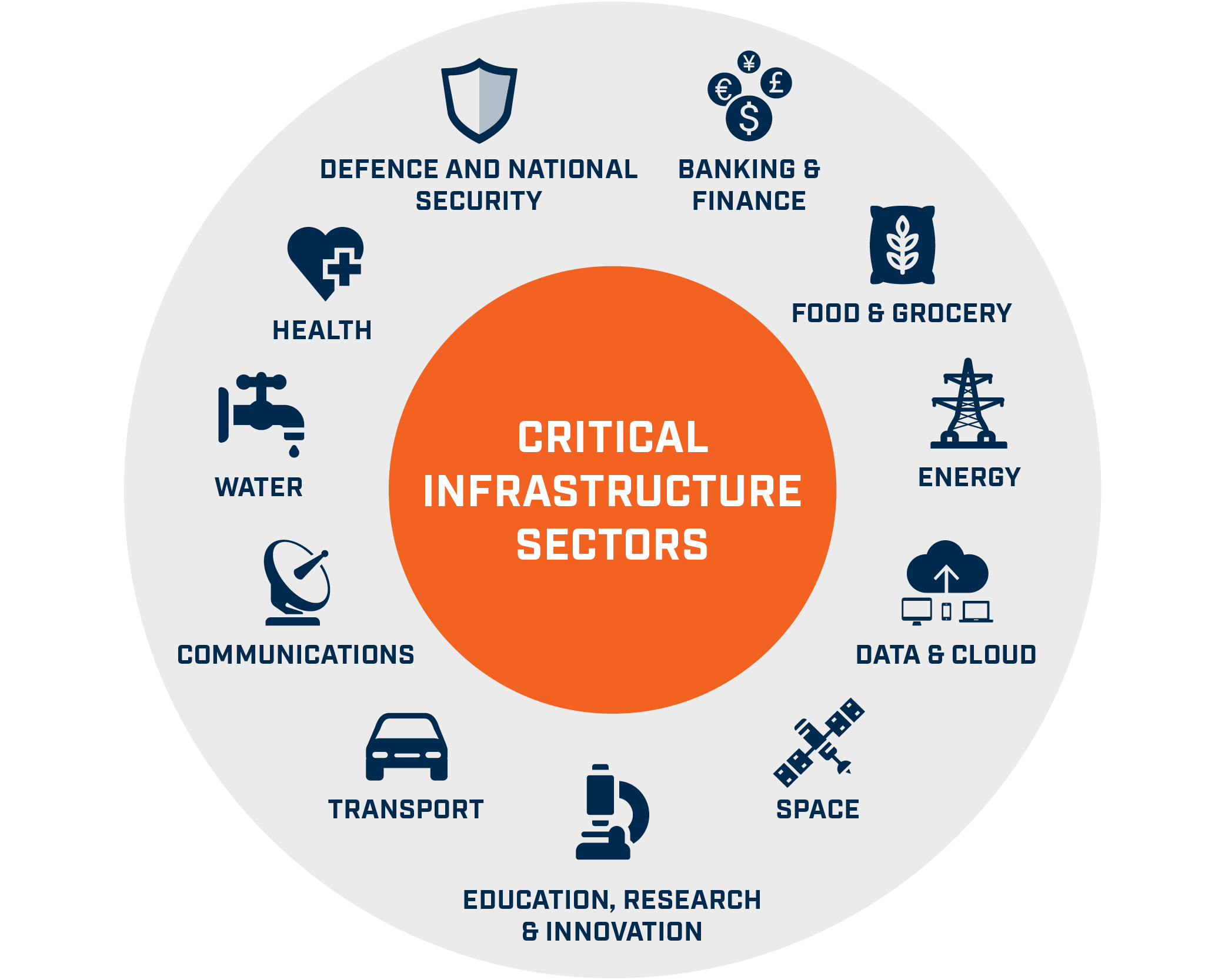
Critical Infrastructure (CI) are the assets, systems, and networks, whether physical or virtual, which are essential for the functioning of a society or economy.
CIs include energy, telecommunications, water supply systems, transportation, banking and finance, emergency services, both governmental and private. These are dynamic, large-scale, complex, spatially distributed and data-rich systems. Damage to one of these systems, their destruction or disruption by natural disasters, terrorism, criminal activity or malicious behaviour, may produce a weighty negative impact for the security and wellness of citizens and being aggravated by the existence of dependencies among different infrastructures.
For instance, an outage occurring in electrical distribution network can produce disruptions for the telecommunication services which in turn may alter the normal functioning of banking services in a specific area thus causing cascading negative effects for the citizens.
Threats to CIs are increasingly growing and constantly evolving. These threats defined as generally initiating events that ignite crisis scenarios may be nature actions, industrial systemic disruptions and malicious actions. As long as man walks the globe, malicious actions shall continue to grow and take different form and shape. Malicious actions are at record highs according to recent reports. It is mind-boggling that there is a hacker attack every 39 seconds.
Around the globe, several government and international authorities have recognized the urgent importance of CIs protection and resilience. They have implemented policies with respect to CI at sectoral and cross-sectoral levels. This has been evidenced by funding research in universities, national laboratories, and private companies in regard to modelling, simulation and analysis of CI dependencies. This has further led to much groundbreaking and varied work.
Government and international institutions recognised that to manage the complexity of these problem at hand there is the need to develop new methodologies, paradigms and tools. For example, in 1998, the United States government recognised the need. The Presidential Policy Directive No.63 on Critical Infrastructure Protection (CIP) recognised the need to address vulnerabilities of CI and need for flexible, evolutionary approaches that span both the public and private sectors, and protect both domestic and international security. Many governments have already recognised the need and acted. Given our greater dependence on ICs, all stakeholders ought to correctively direct their efforts towards ICs security.
Steven Kakaire




